New: The startup CTO's field guide to running security
Read the guide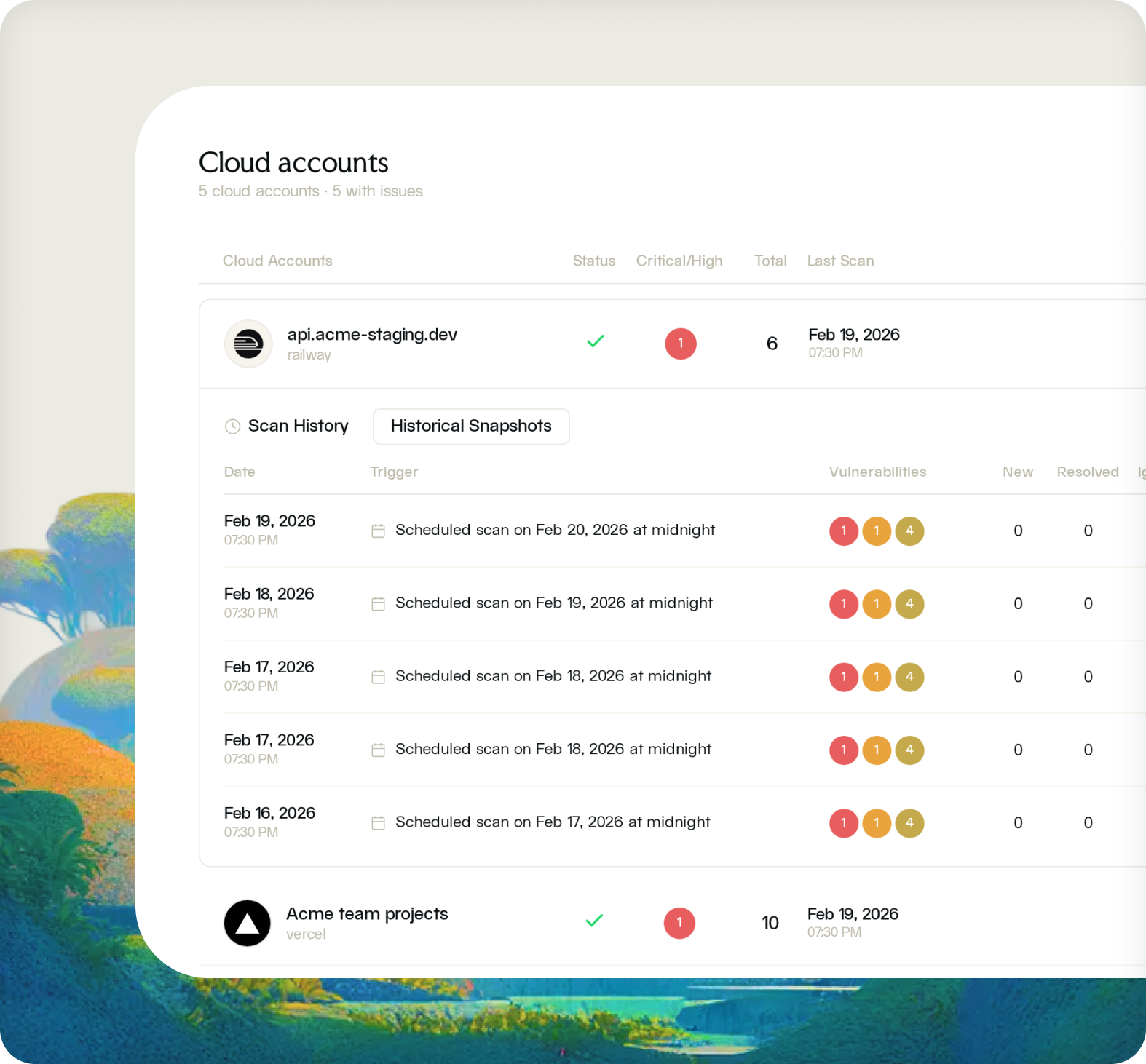
Fencer continuously monitors your cloud infrastructure for misconfigurations, scans your IaC before deployment, and checks every container image for vulnerabilities. One platform, no security team required.
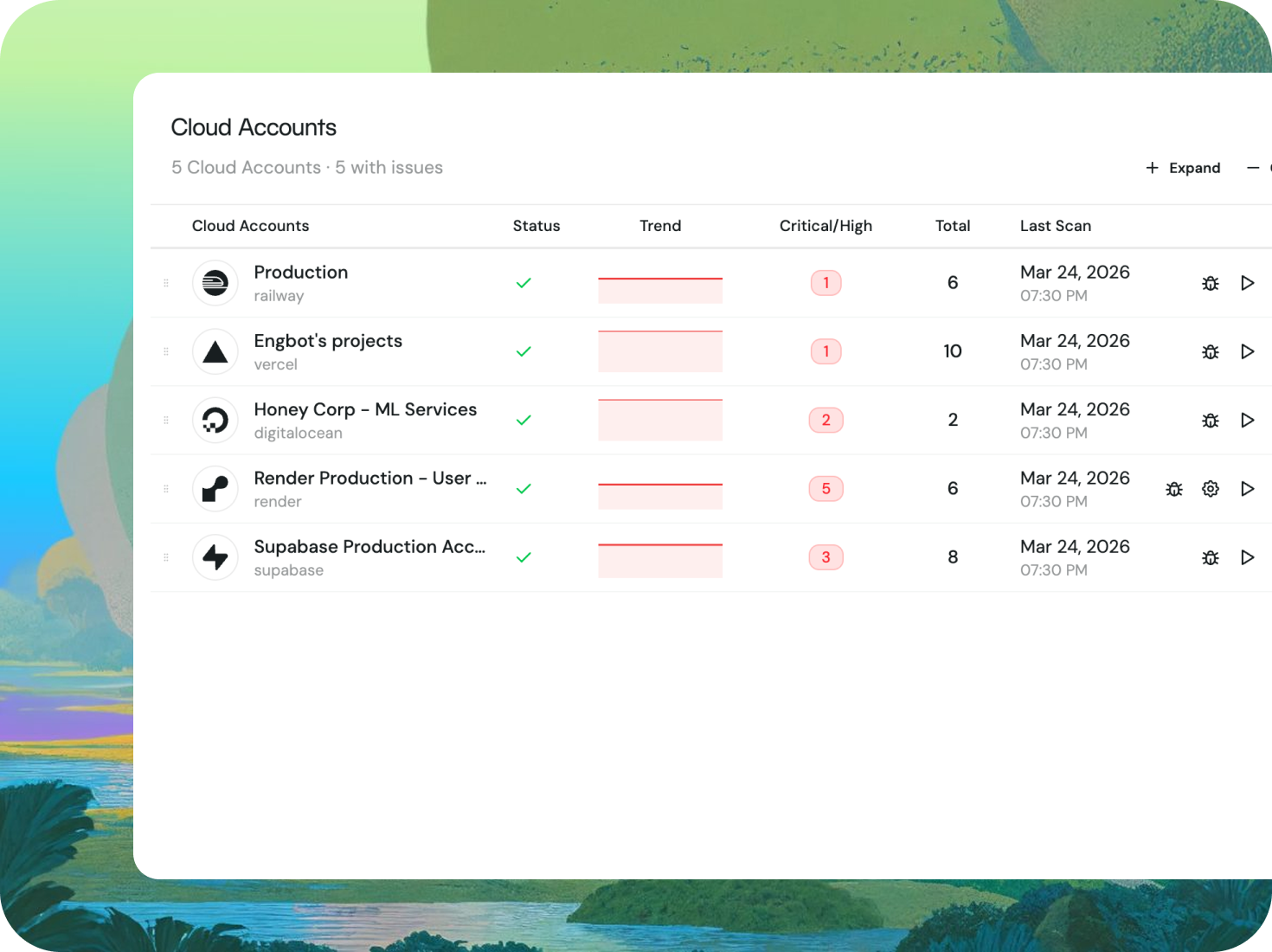
Fencer continuously audits your cloud configuration against security best practices, surfacing misconfigurations before they become incidents. Connect your cloud accounts and see findings immediately, with remediation guidance included.
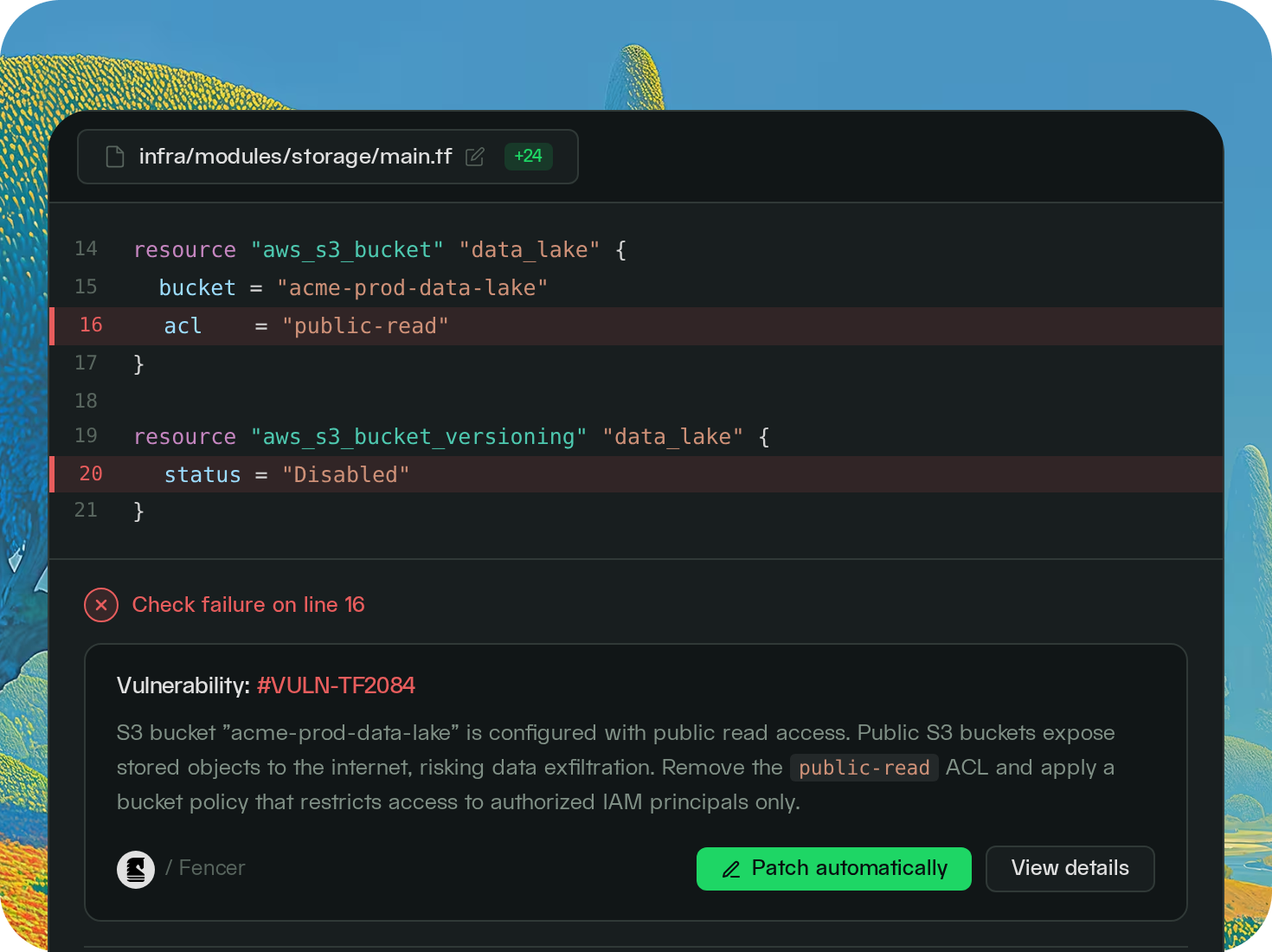
Fencer scans your Terraform and other IaC files in every pull request, flagging misconfigurations before they reach your cloud environment. Fix it in code, not in production.
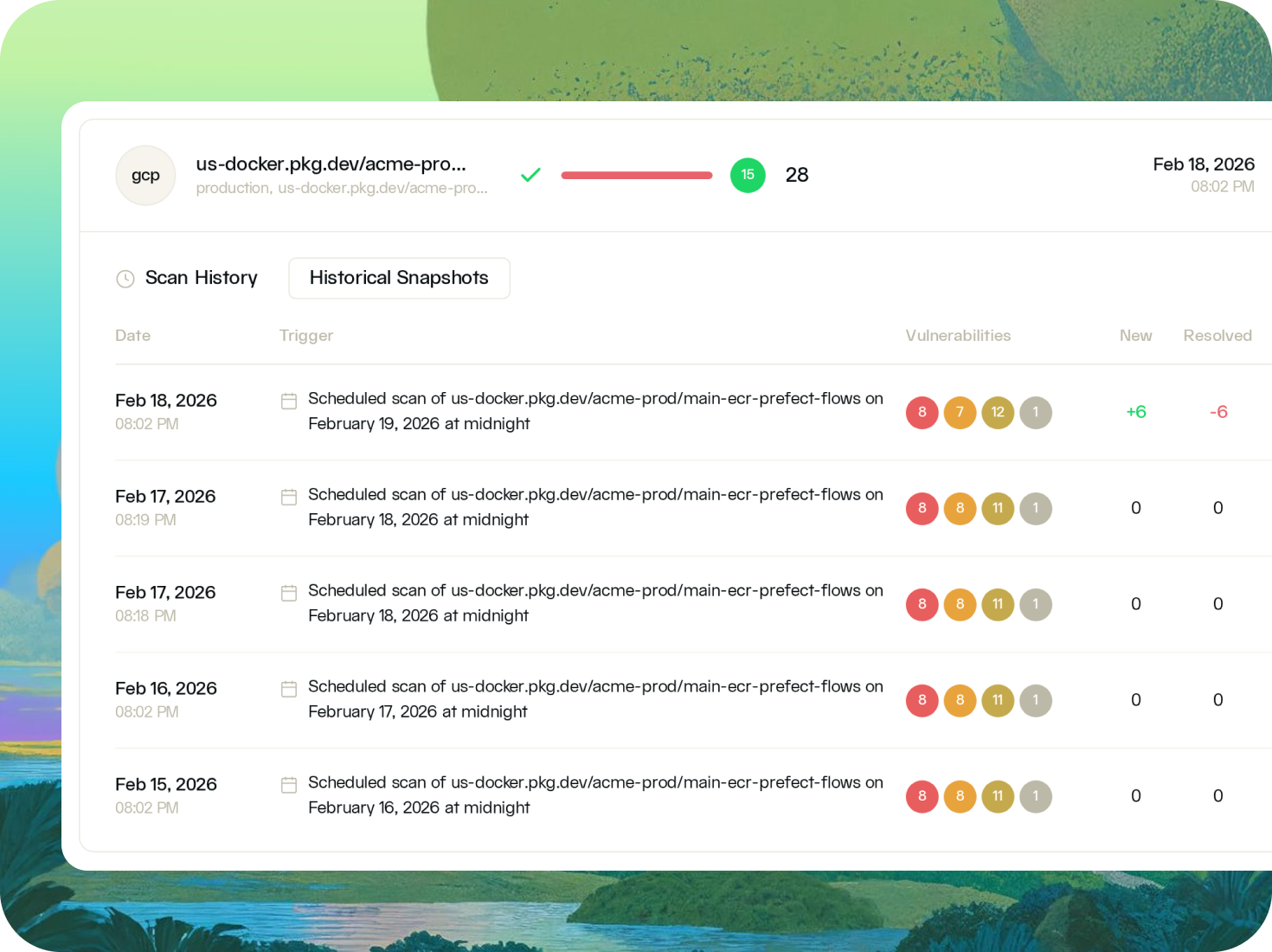
Fencer scans your container images and build artifacts for vulnerabilities, secrets, and dependency risks before they reach production. Know what's inside everything you deploy.
Open S3 buckets, overpermissioned IAM roles, and disabled encryption are among the most common causes of cloud breaches. Fencer surfaces these continuously, not just at audit time.
IaC scanning ensures that security misconfigurations are flagged in code review before they deploy. Your standards get enforced at the point where it is cheapest to fix them.
SOC 2 and other complince frameworks require continuous monitoring, documented remediation, and evidence of your cloud security posture. Fencer generates this evidence automatically as you work.
Container images accumulate vulnerabilities over time. Fencer scans every image before deployment and flags known vulnerabilities with severity ratings and fix guidance.

— Ben Papillon
CTO & Co-founder, Schematic