New: The startup CTO's field guide to running security
Read the guide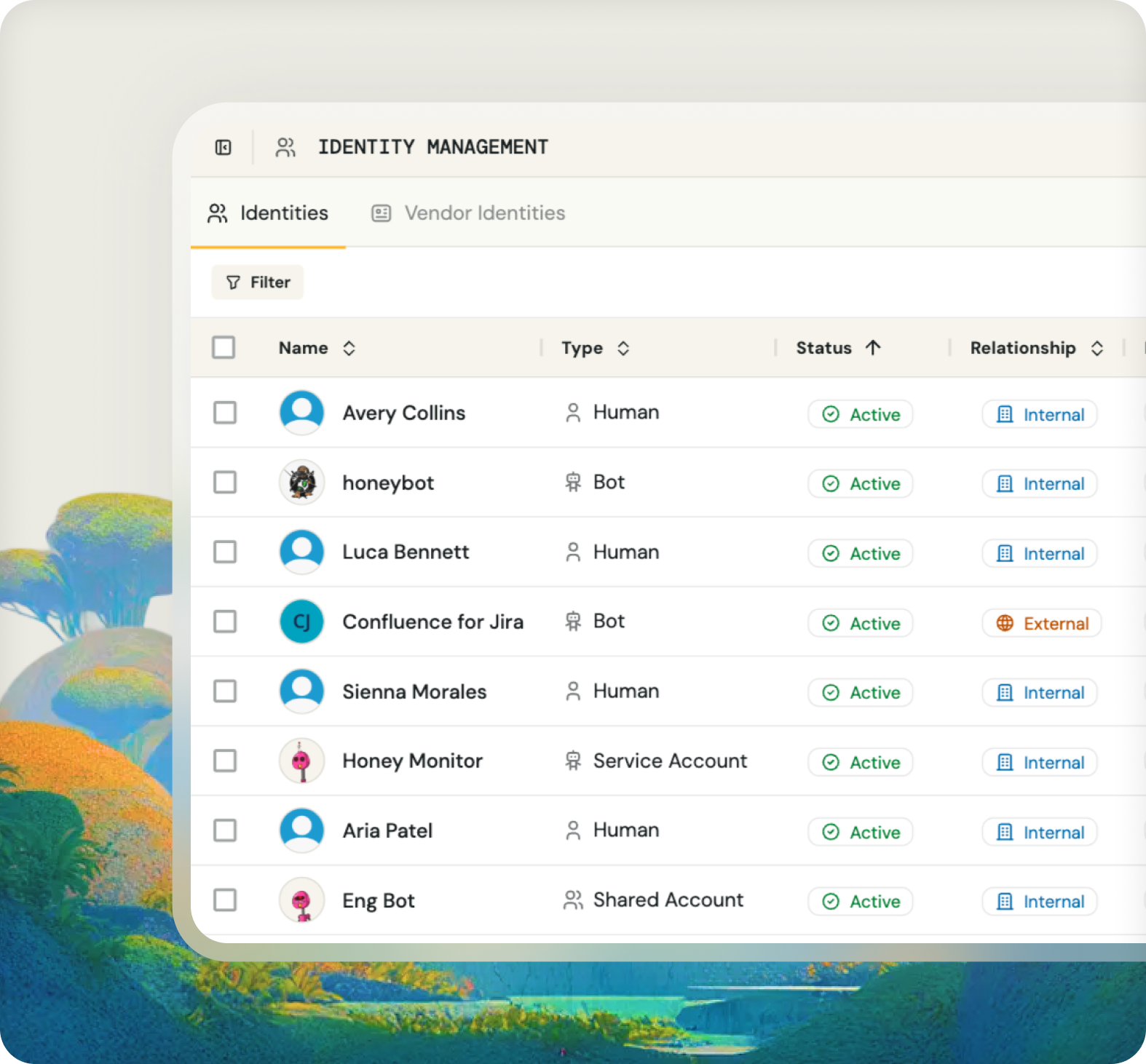
See who has access to what across all your tools. Automate account discovery, flag issues, and export audit-ready evidence for SOC 2, ISO 27001, and other compliance frameworks.
Fencer auto-discovers accounts across your connected services, so you can review access without logging into 20 different tools and manually assembling reports.
.png)
See not just who has an account, but what level of access they have.
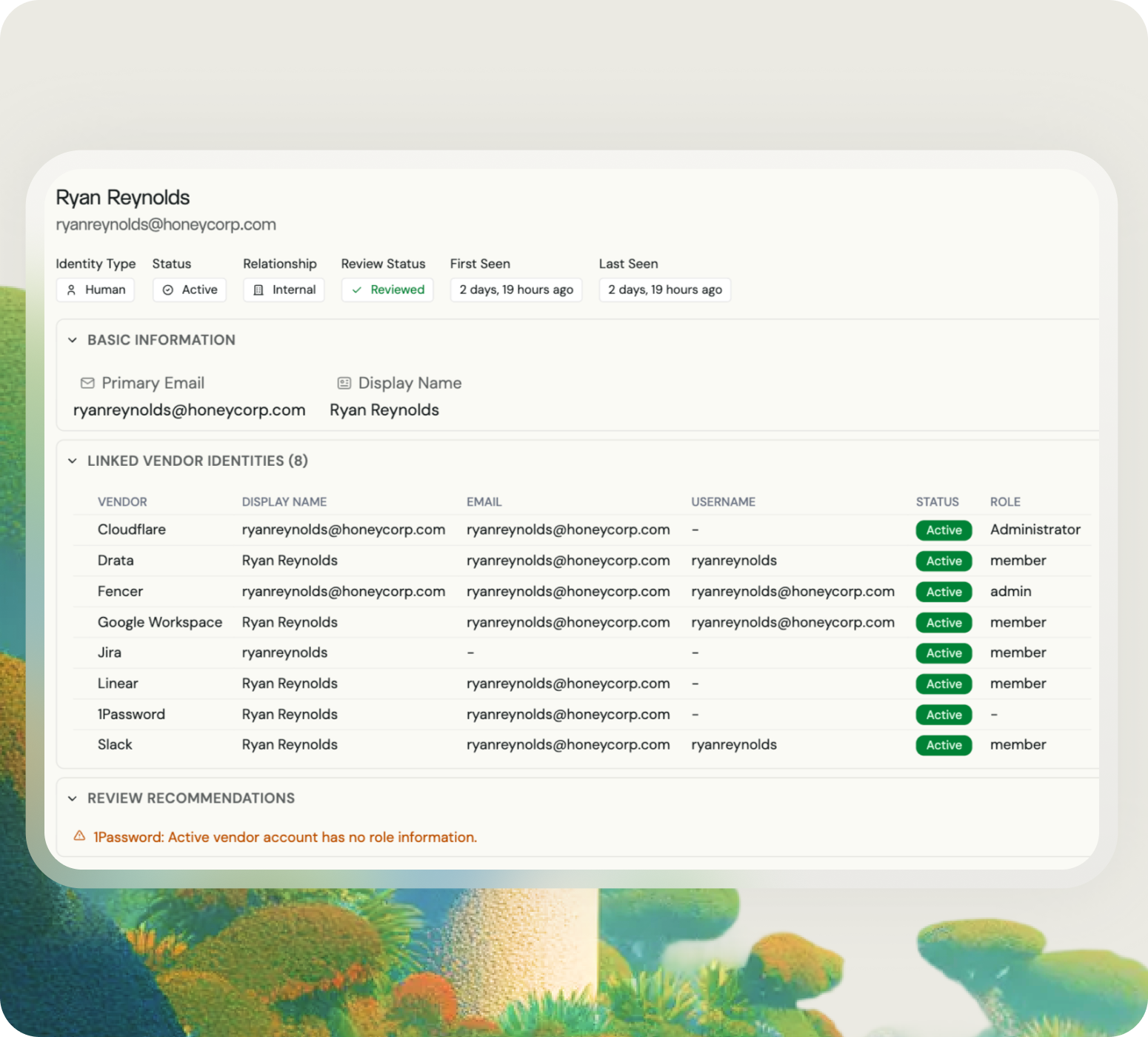
Fencer surfaces potential access issues so you can address them before they become security risks.
.png)
Generate compliance documentation instantly. Exportable CSV reports support user access review requirements for SOC 2, ISO 27001, and other audits
.png)
SOC 2, ISO 27001, and other compliance frameworks require regular user access reviews. Fencer automates the account discovery and evidence generation, reducing review time from days to minutes.
When someone leaves your company, see all their accounts across every connected service in one view. Confirm access was revoked and document the offboarding for compliance.
Accounts that should have been deprovisioned are a common security gap. Fencer shows active/inactive status and last login dates so you can spot accounts that shouldn't exist.
Service accounts, API keys, and bot integrations often go unreviewed. Fencer discovers non-human identities alongside employee accounts so nothing falls through the cracks.

— Ben Papillon
CTO & Co-Founder, Schematic