New: The startup CTO's field guide to running security
Read the guide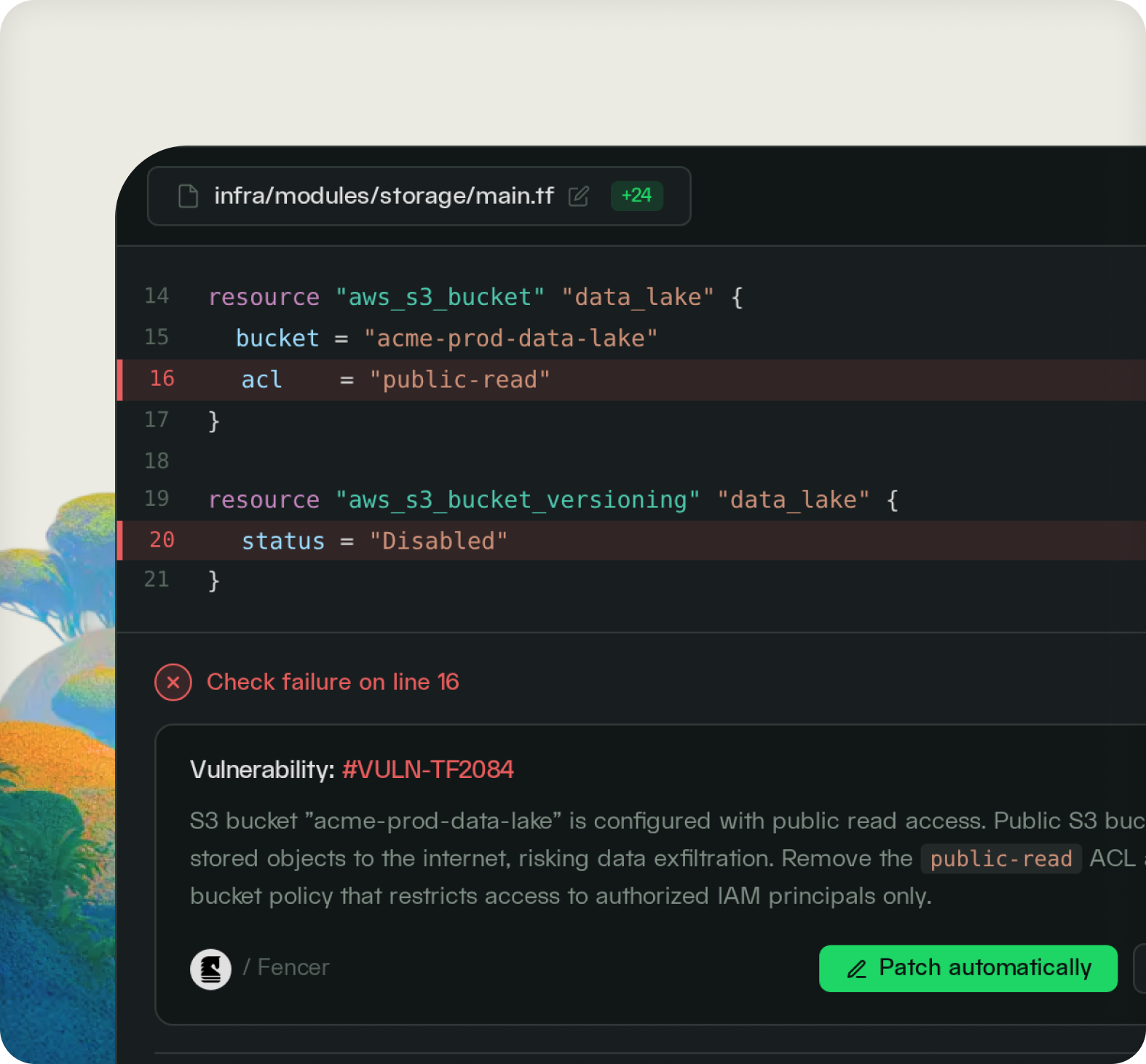
Fencer scans Terraform, CloudFormation, Kubernetes, Helm, and Azure ARM on every PR. Misconfigurations surface as inline annotations before anything reaches your cloud accounts.
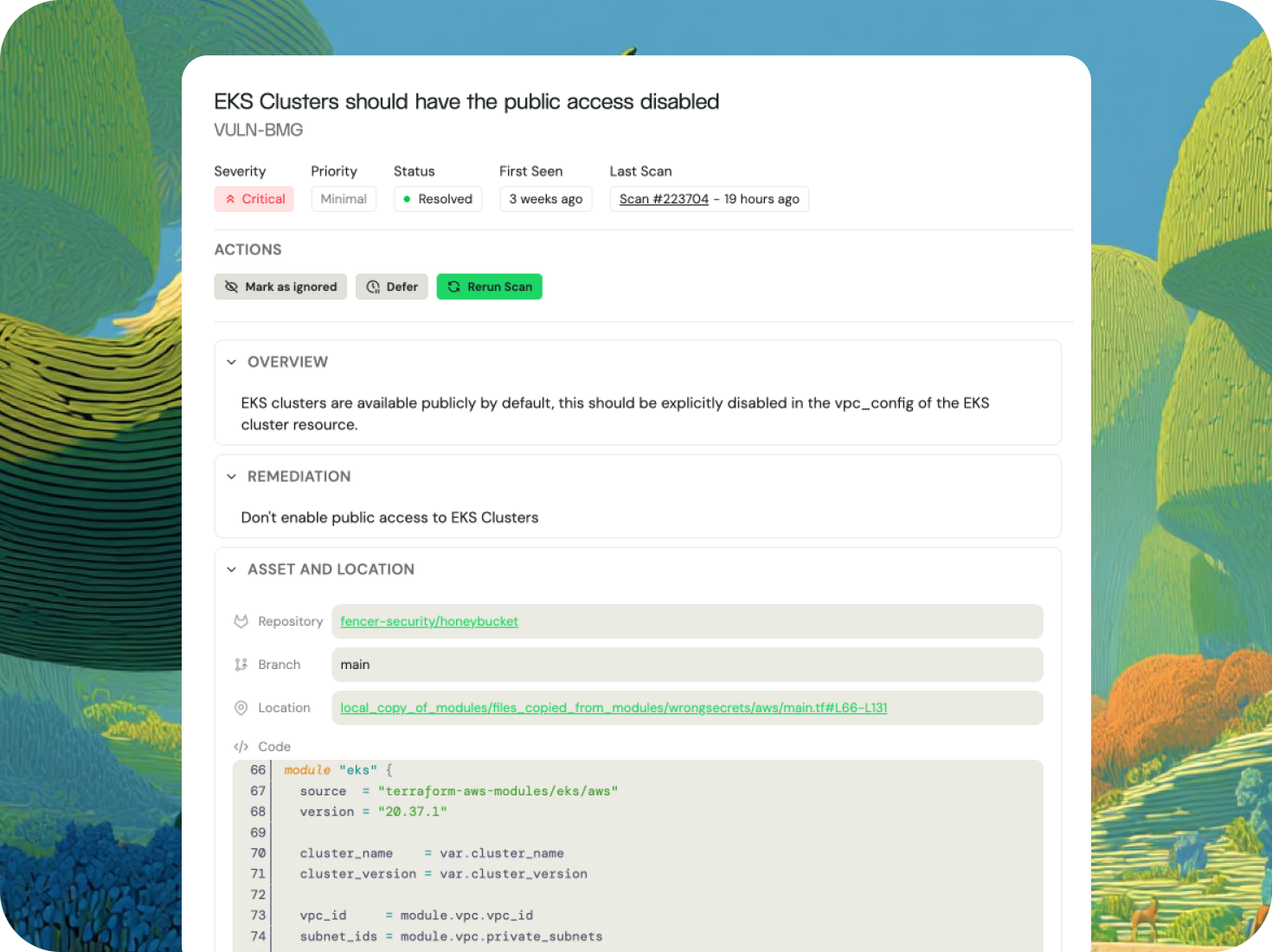
Fencer scans IaC templates as part of its standard code scanning workflow, triggered on every pull request and on a daily schedule.
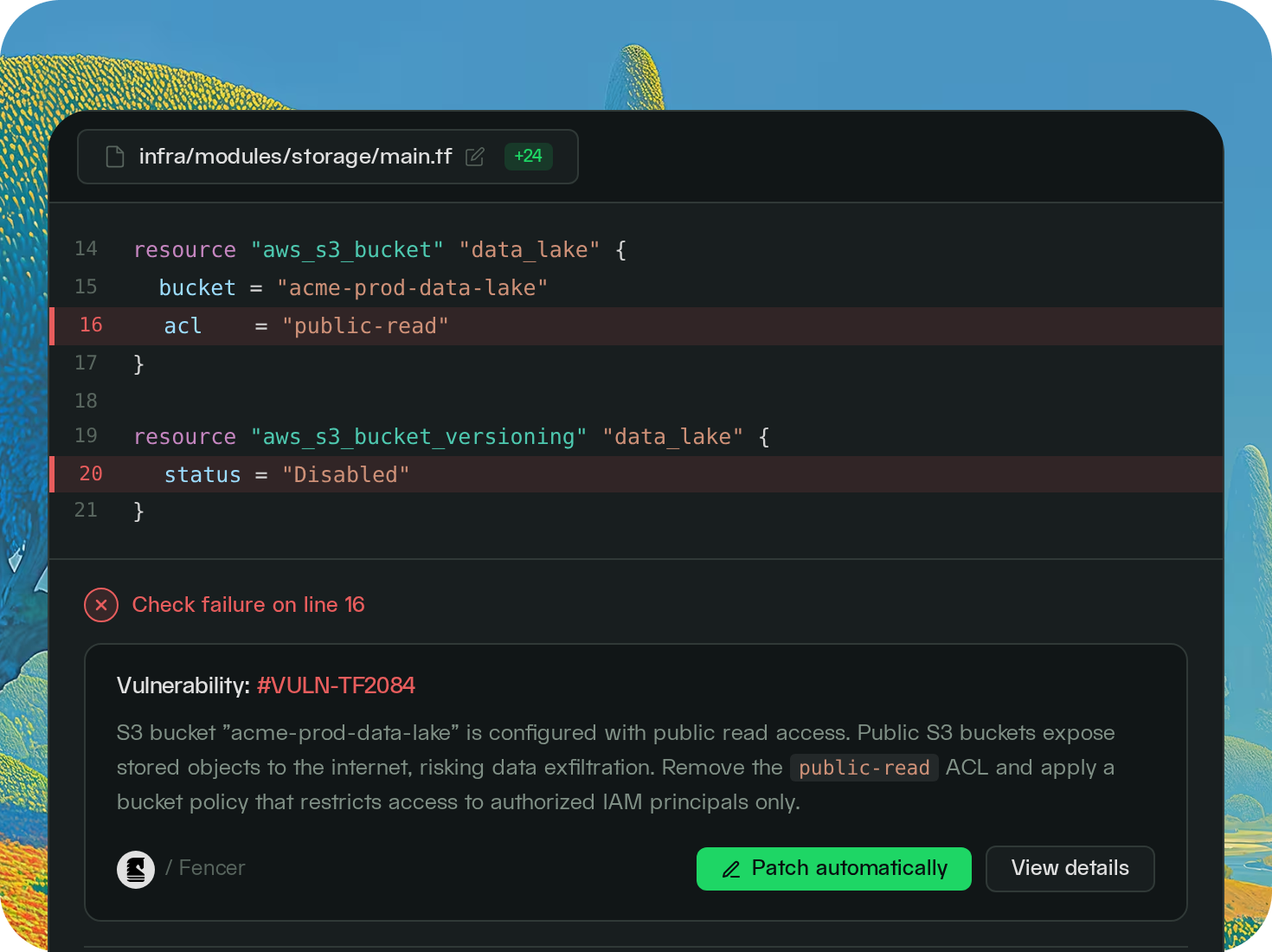
When Fencer detects a misconfiguration in an IaC template, it surfaces an inline annotation on the exact line that introduced it. You can then trigger an AI fix agent to generate a patch and open a pull request so the issue is resolved without leaving your workflow.
Fencer's IaC scanning checks for misconfigurations across the same categories it monitors in live cloud accounts: IAM, storage, encryption, networking, compute, and database. The same issues that CSPM finds in production can be caught in your templates before they're ever deployed.
.png)
A Terraform file with a public S3 bucket or permissive IAM role will deploy exactly as written. Fencer flags it in the PR so it never makes it to your cloud account.
SOC 2 auditors increasingly ask about pre-deployment infrastructure controls, not just runtime monitoring. Fencer's scan history shows every IaC check that ran, when it ran, and what it found.
Every new Terraform module and CloudFormation template gets scanned automatically. Make security the standard as your cloud footprint grows.
CSPM monitors your live infrastructure. IaC scanning covers what gets deployed into it. Together, they close the loop on cloud misconfiguration from code to production.

- David Merritt, CTO, Watch Duty