New: The startup CTO's field guide to running security
Read the guide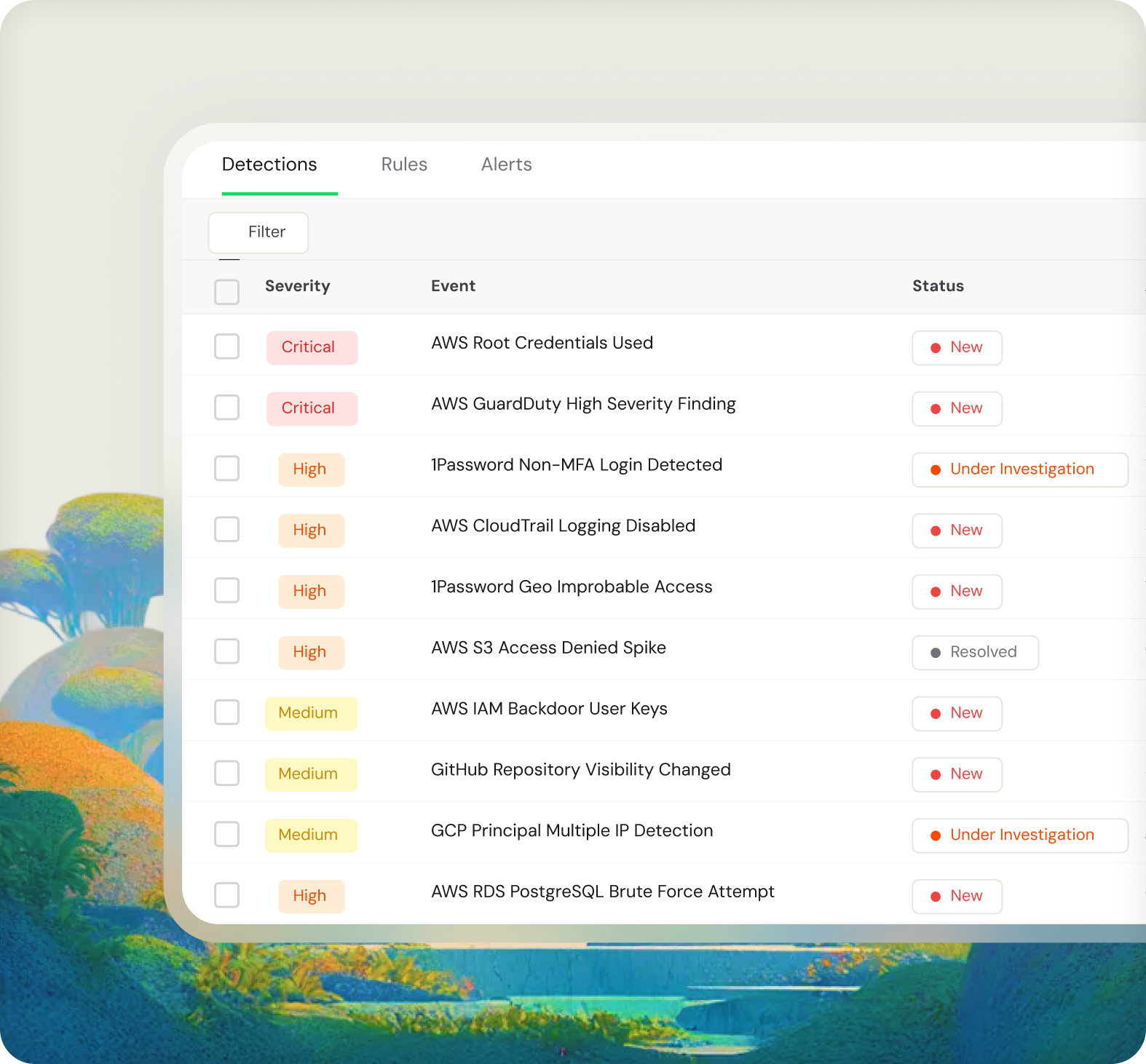
Real-time security monitoring with pre-built detection rules, configurable alerts, and a log explorer for threat hunting. Connect your cloud infrastructure and start detecting threats in minutes.
Fencer continuously monitors your connected cloud services and flags security events as they happen. No manual log reviews required.

Every detection rule comes with a description of what it catches, why it matters, and what to do about it. You don't need to be a security expert to respond appropriately.

Route alerts to the right people through the right channels. Set up multiple alert configurations for different scenarios, from real-time critical alerts to daily digests.

When you need to dig deeper, the threat hunting log explorer gives you full access to your security events. Search across all ingested logs, filter by source or message content, and export raw data for external analysis.
.avif)
AWS root credential usage, CloudTrail changes, unusual access patterns, failed authentication spikes. Fencer flags events that could indicate an attack in progress or a policy violation.
SOC 2 and other frameworks require continuous monitoring, detection, and incident response capabilities. Fencer provides documented evidence that you're actively watching for threats, not just hoping nothing bad happens.
When something looks suspicious, use threat hunting to search your logs, filter by time range or data source, and drill into the raw event data. No switching between cloud consoles or piecing together logs manually.
1Password logins without MFA, geo-improbable access, unusual client detection. Fencer monitors your identity provider for signs of account compromise or policy violations.

— Jason Byck
CTO, Renew