New: The startup CTO's field guide to running security
Read the guide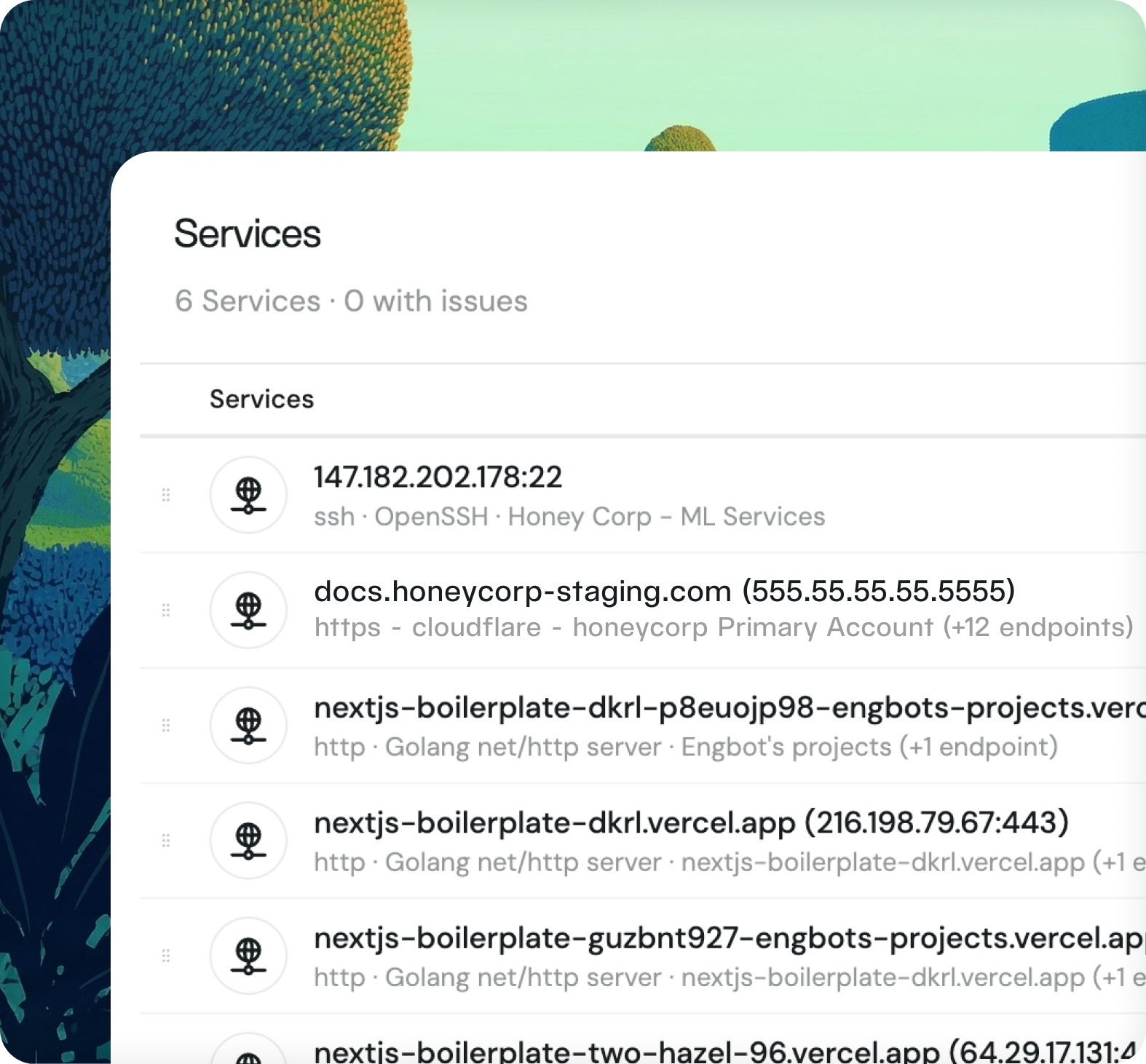
Fencer discovers open ports and exposed services across your public IPs, then checks each for known vulnerabilities. Connect your cloud account and start scanning instantly.
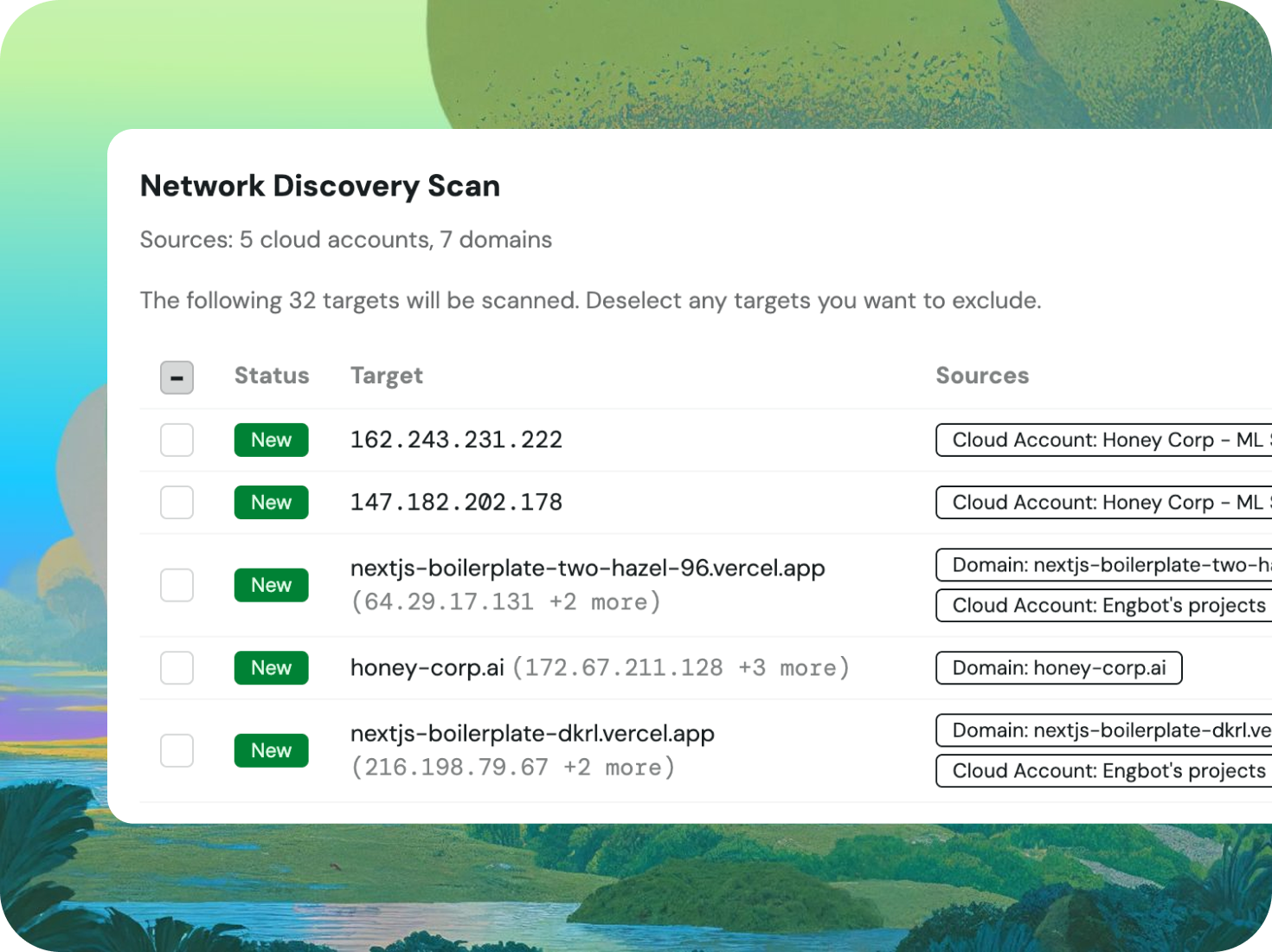
Fencer connects to your cloud accounts and domains and automatically extracts public IP addresses from EC2 instances, load balancers, RDS databases, and Redshift clusters. It then runs a port scan across the top 1,000 ports on each IP, recording every open service it finds.
Once open services are discovered, Fencer automatically runs vulnerability checks against each one. Findings flow directly into your vulnerability pipeline with severity ratings and remediation guidance. Every service has a full scan history so your team can track whether things are getting better or worse over time.
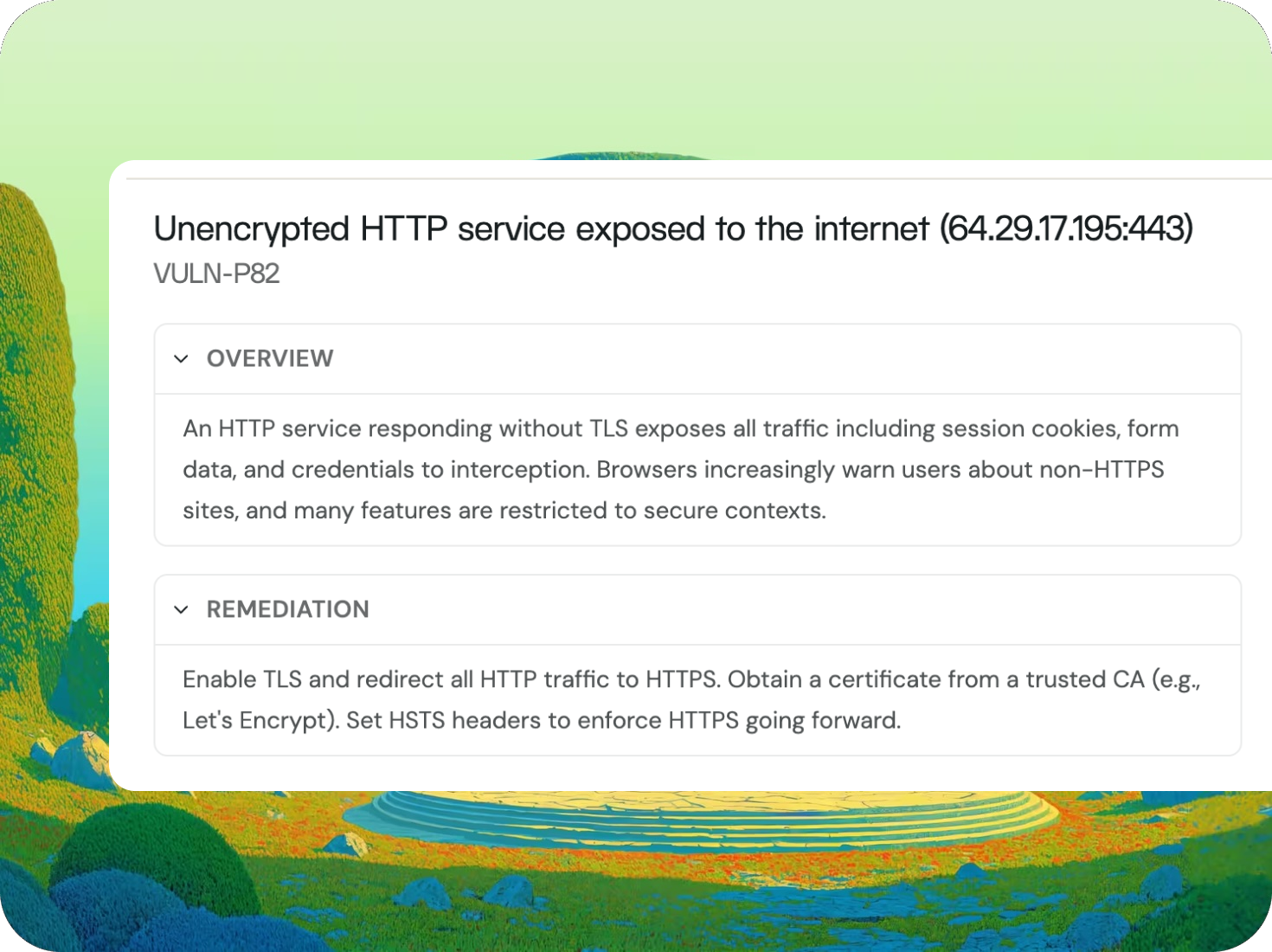
Fencer scans from the outside in, surfacing open ports, exposed services, and known vulnerabilities on your public IPs before an attacker finds them.
An unauthenticated Redis or publicly accessible database is a breach waiting to happen. Fencer flags these as Critical findings immediately on first scan.
SOC 2 auditors ask for external vulnerability scanning evidence on production infrastructure. Fencer's nightly scan history and findings record give you that automatically.
New EC2 instances and load balancers are picked up automatically from your cloud account. Coverage grows with your infrastructure, without any manual updates.

— David Merritt
CTO, Watch Duty