New: The startup CTO's field guide to running security
Read the guide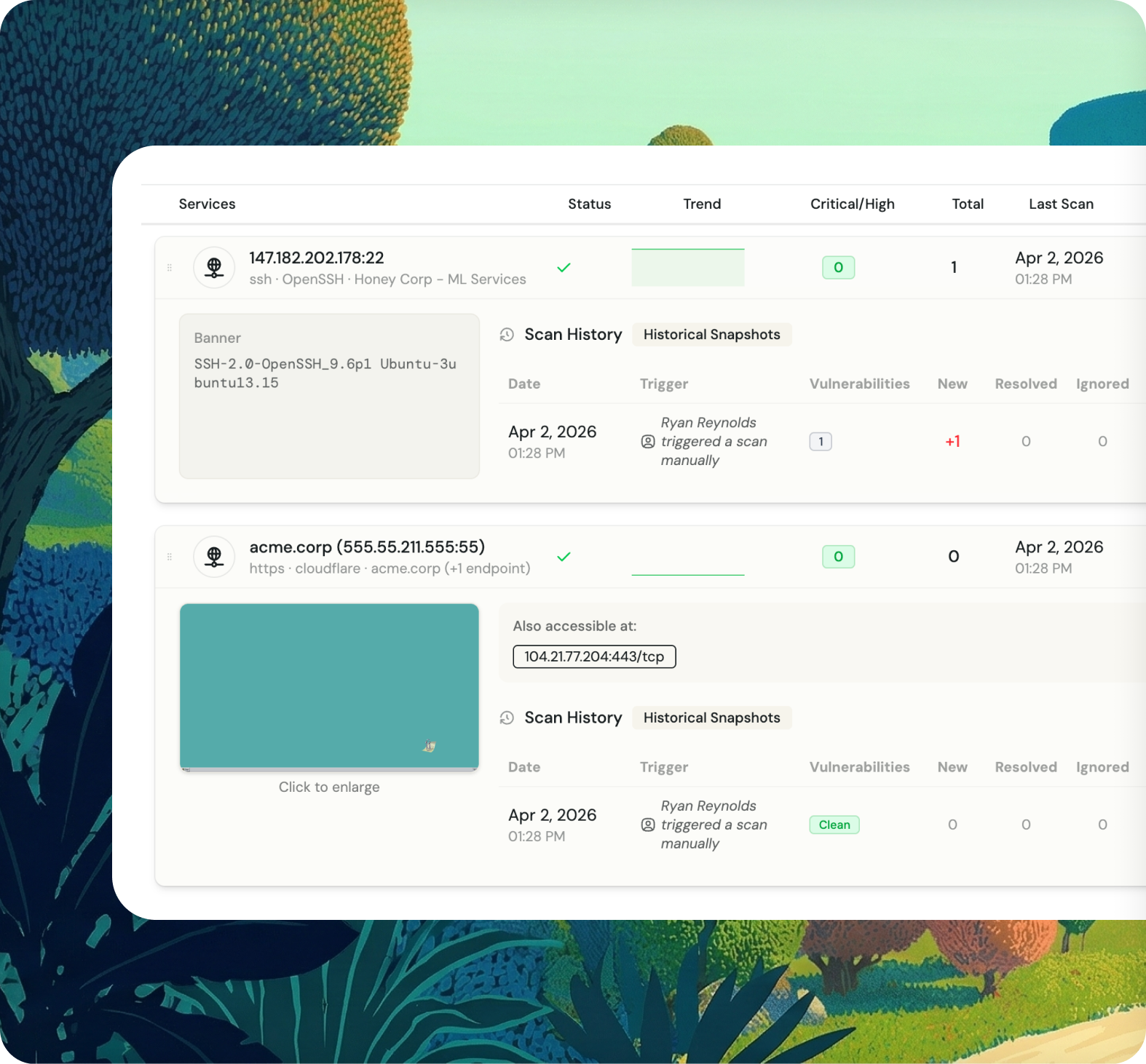
Fencer monitors everything visible from the outside: your domains, DNS records, SSL certificates, email authentication, lookalike phishing domains, open ports, and exposed network services. Updated daily, findings in one place.
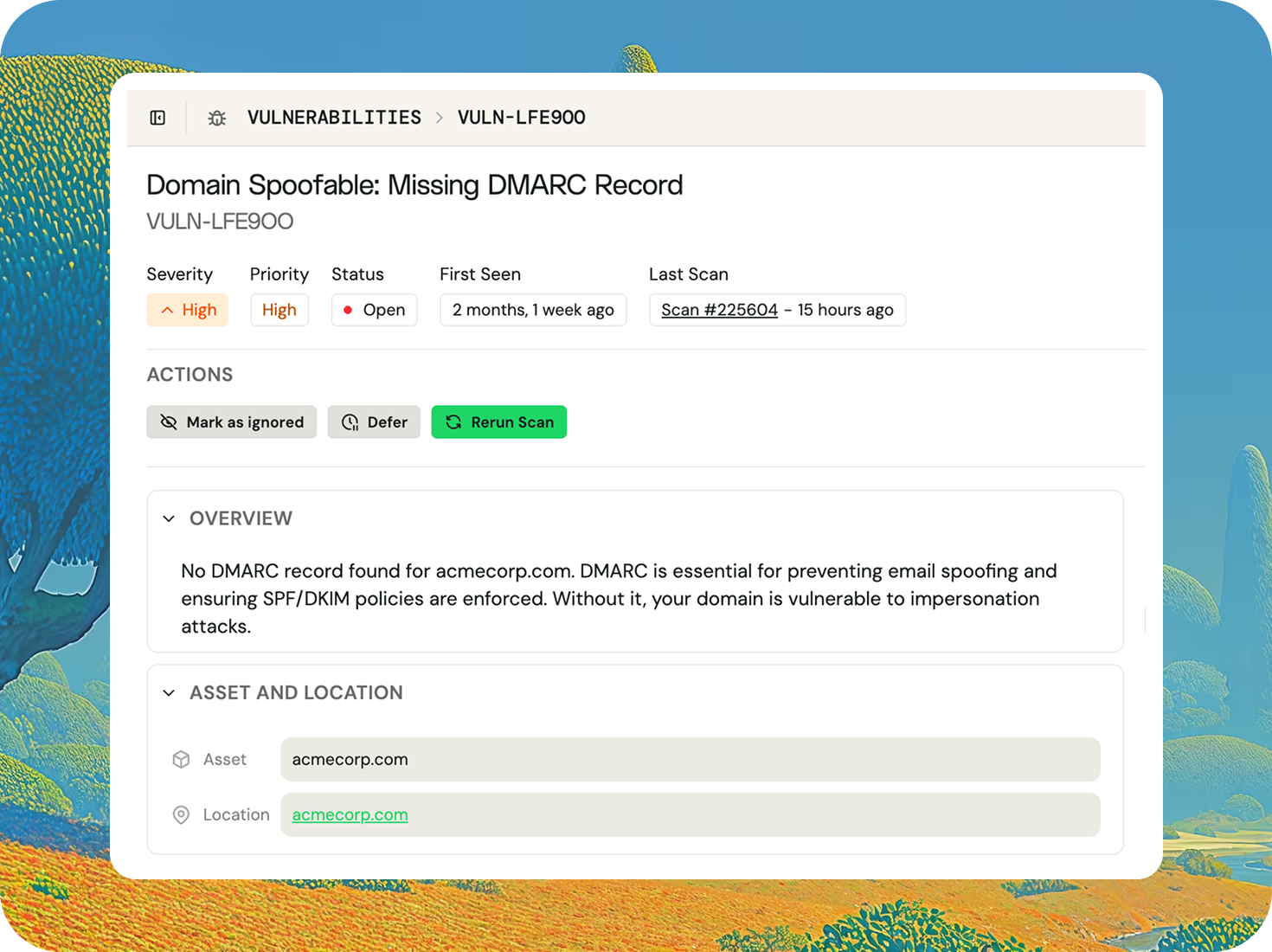
Fencer scans your domains daily across six layers: DNS record health, SSL/TLS certificate analysis, email authentication validation (SPF, DMARC), spam blacklist checking, lookalike phishing domain detection, and subdomain discovery. One scan, everything visible about your domain.
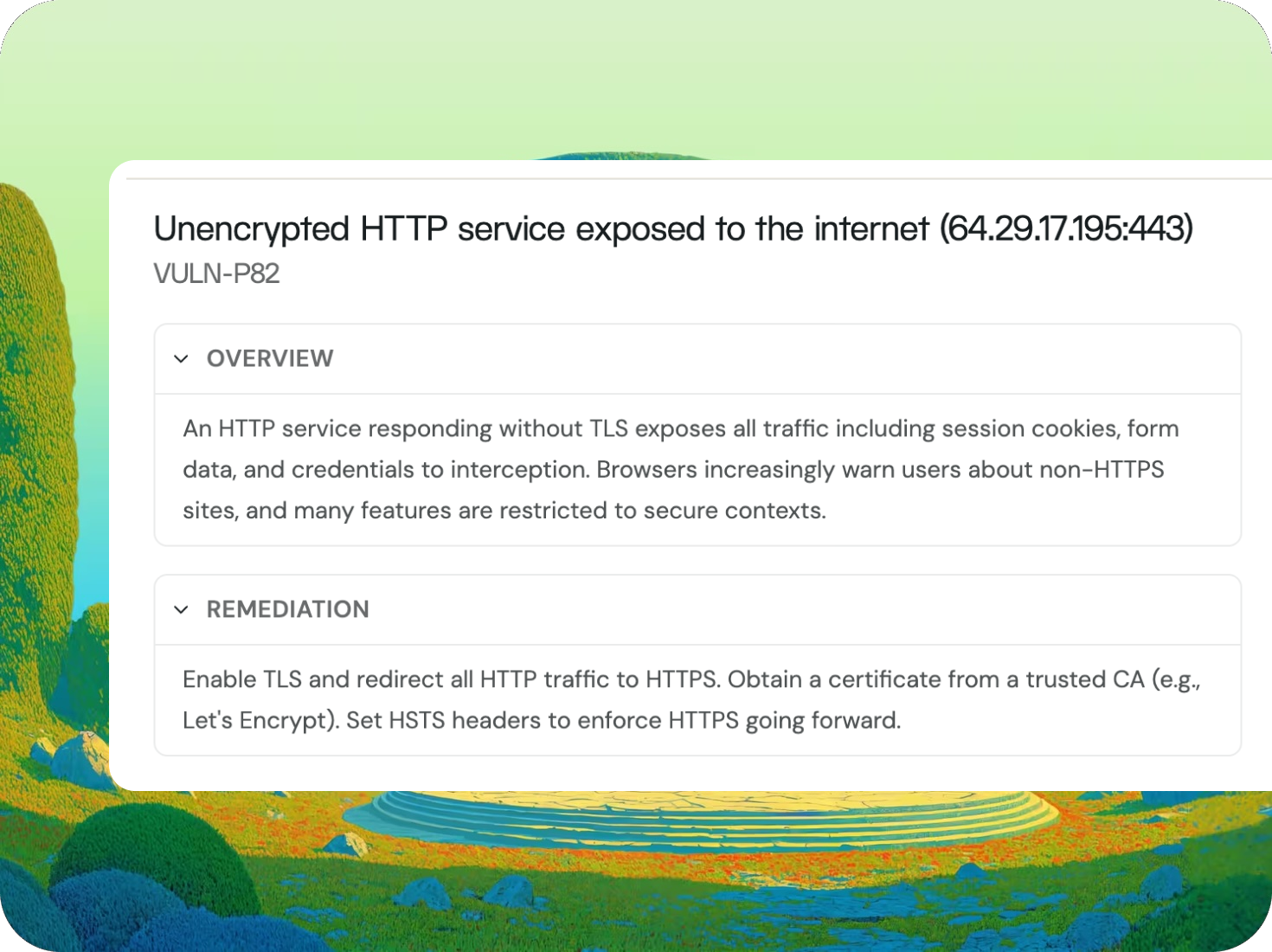
Fencer connects to your cloud accounts and domains, automatically discovers every public IP and open port, then runs vulnerability checks against each service it finds. Findings flow into your vulnerability pipeline with severity ratings and remediation guidance.
Fencer discovers every open port, exposed service, and lookalike phishing domain targeting your brand. Updated daily so your perimeter reflects the current state of your infrastructure.
SSL certificates expire, DMARC policies go stale, and subdomains accumulate without anyone noticing. Fencer catches all of it on a daily schedule so nothing slips through.
SOC 2 auditors ask about domain monitoring, email authentication, and network vulnerability scanning. Fencer's daily scan history gives you documented evidence across all three.
A separate SSL monitor, a DMARC tool, a port scanner — each with its own dashboard and alerts. Fencer covers your full external perimeter in one place.

— Ben Papillon
CTO & Co-founder, Schematic