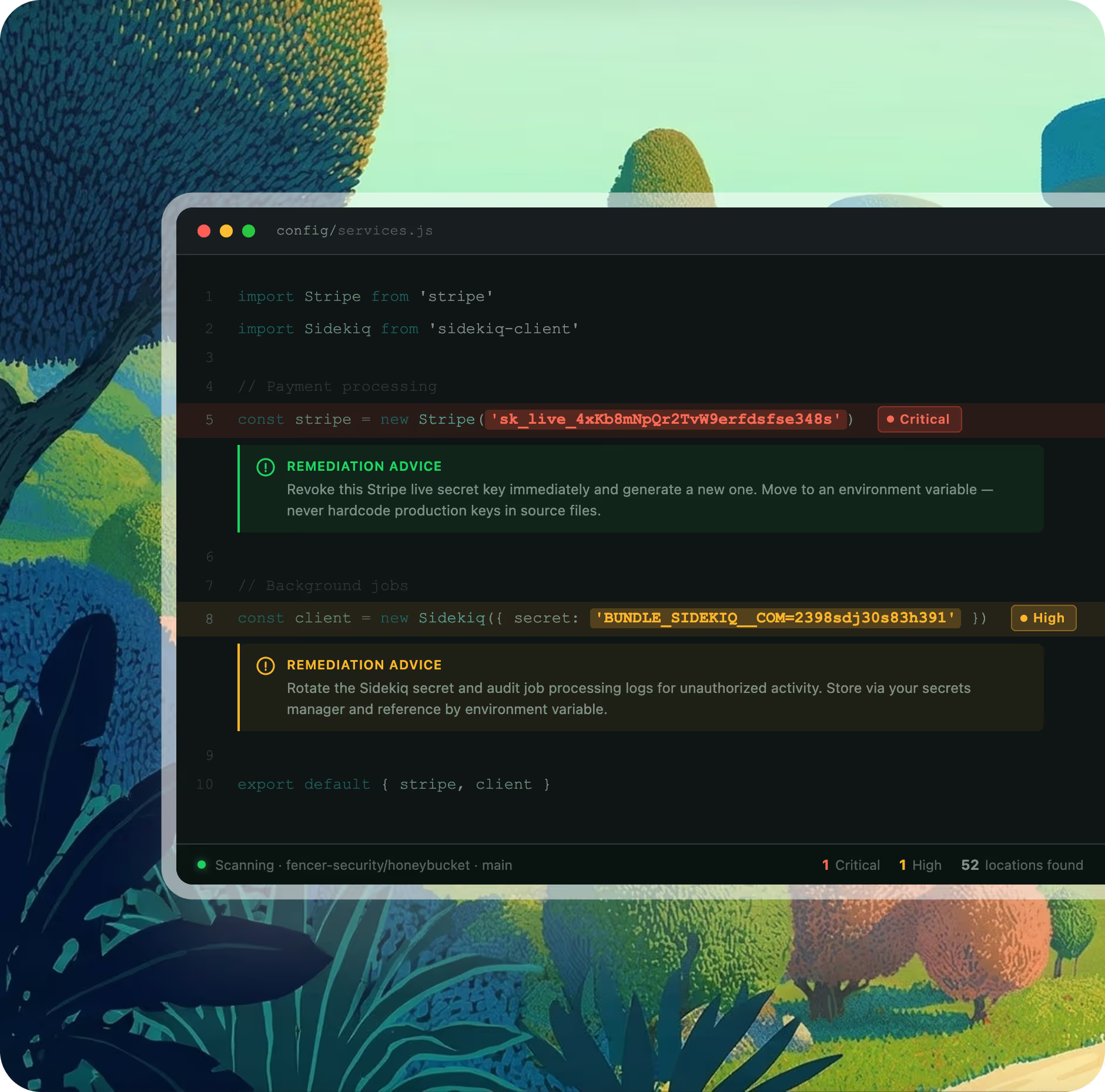
Fencer scans your entire codebase and hosting platforms for exposed API keys, tokens, private keys, and hardcoded credentials. Every new pull request is checked automatically. Every finding comes with specific guidance on what to fix and how.
Fencer scans all of your existing code when you connect, and continuously checks every new commit going forward. It also scans hosting platforms including AWS, GCP, Azure, Heroku, Render, and Railway — so exposed credentials surface wherever they live.
Every pull request is scanned for exposed credentials before it merges. Findings surface in your existing workflow, so secrets are caught at the point they're introduced

.avif)
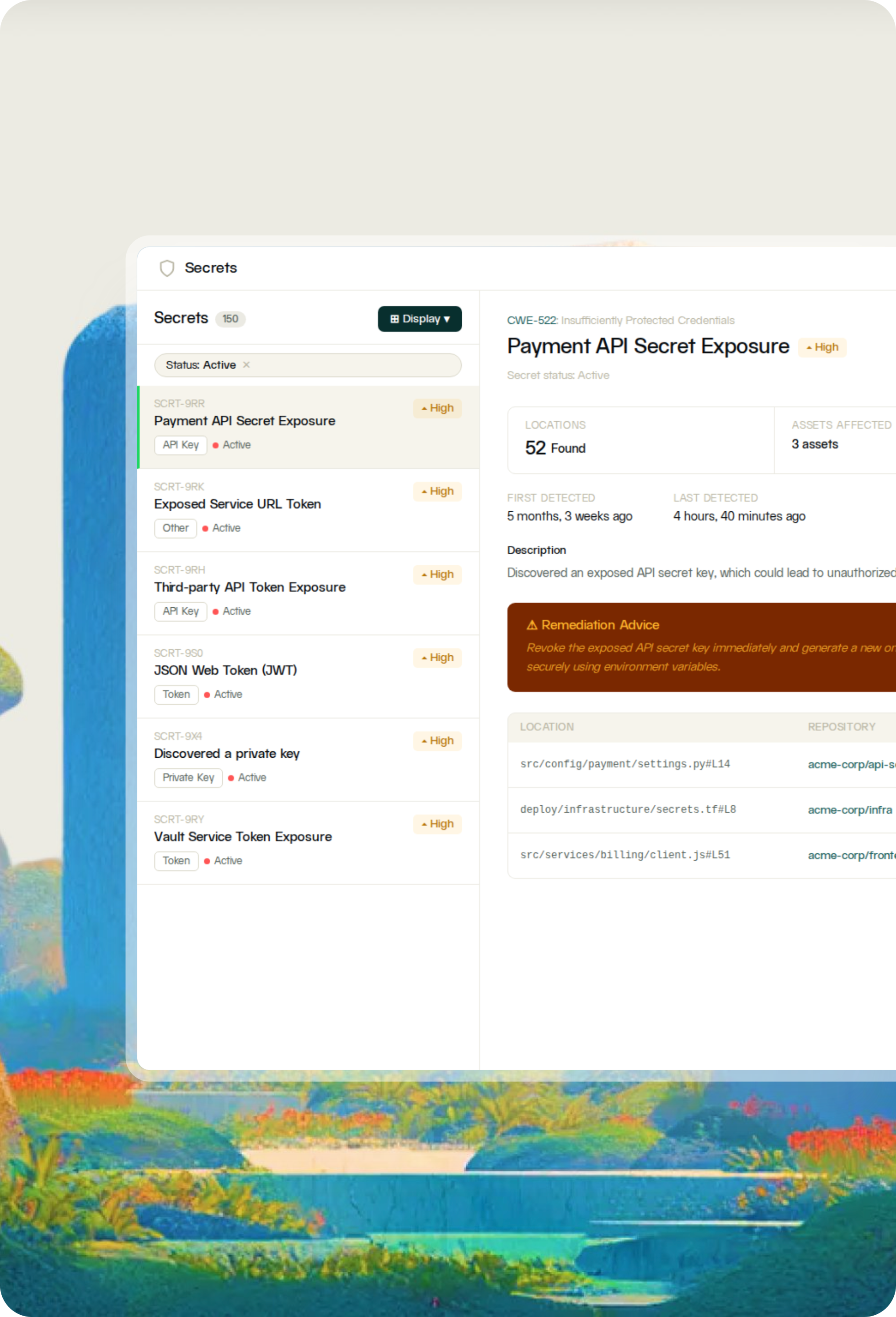
Each finding shows the exact repository, branch, file path, and line of code where a credential was found, along with how many locations it spans and how long it has been present.
.html%201.avif)
Most teams find exposed credentials they didn't know existed when they first connect. Fencer scans your full codebase on day one, not just code going forward.
Pull requests are scanned before they merge. You catch exposed credentials in your existing workflow before anything reaches production.
SOC 2 and other major compliance frameworks require evidence of active credential monitoring, not just policy.
When a secret is flagged, Fencer shows exactly where it is, how long it has been exposed, and what to do next.

— Jason Byck
CTO, Renew