Fencer scans every connected repository and builds a live dependency inventory with license risk scoring, dependency graph visualization, and SBOM export in CycloneDX or SPDX.
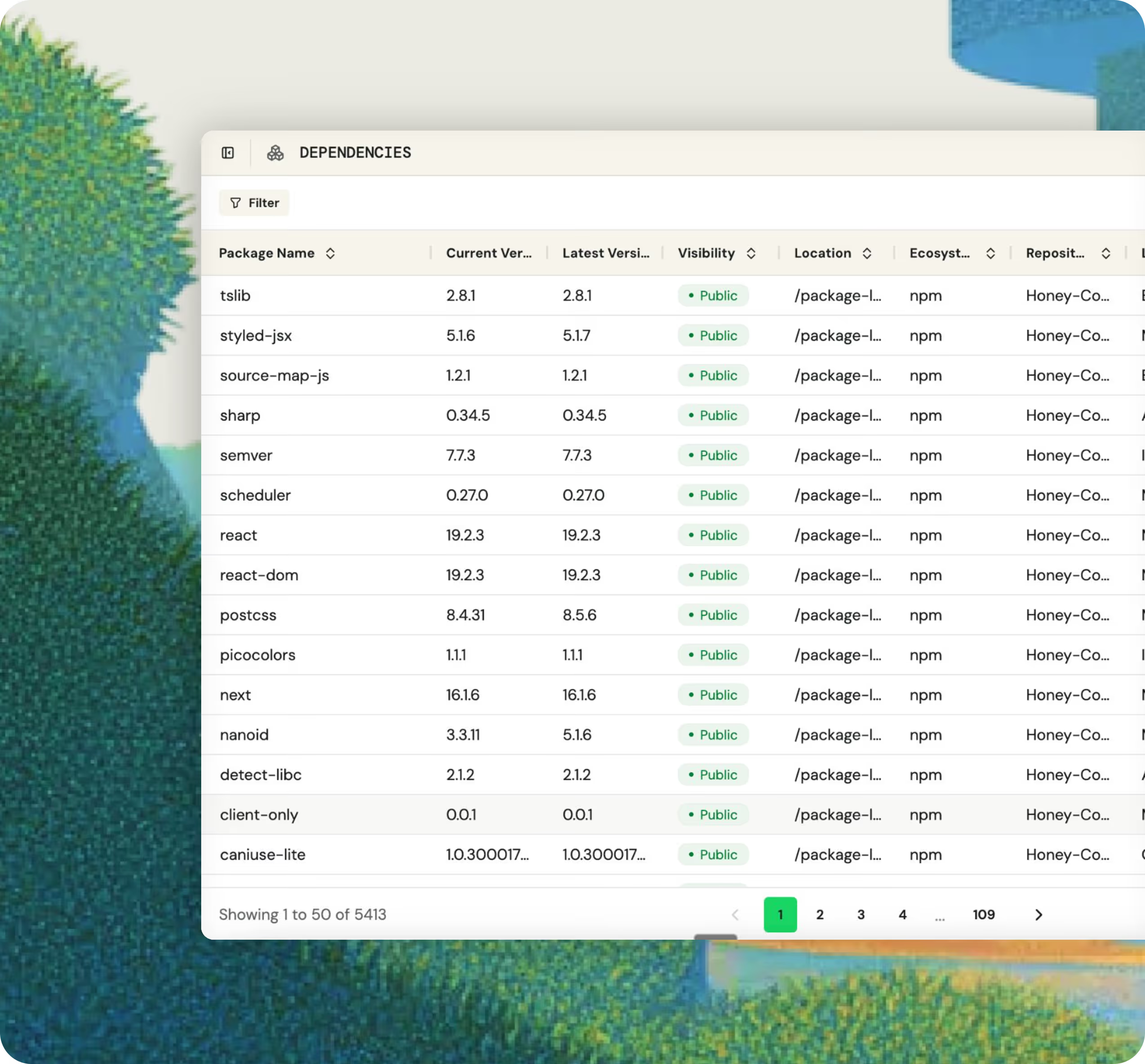
Fencer scans every connected repository and surfaces every dependency (direct, transitive, and root) in a searchable, filterable list. When a CVE drops, you know which repositories are affected before you have to go looking.

Fencer maps how every dependency relates to the rest of your stack, including what transitive dependencies it pulls in. When a vulnerability or license issue surfaces in a shared package, you can see the blast radius without digging through manifests.
Generate a software bill of materials for any connected repository on demand, in Cyclone DX or SPDX format. When a customer, enterprise prospect, or auditor requests a software inventory, you can produce it in seconds.

When a critical vulnerability is disclosed in a popular open source package, Fencer's dependency inventory shows you which repositories are affected so you can triage and act fast.
Enterprise prospects and compliance auditors increasingly ask for a software bill of materials before signing a contract or completing an assessment. With Fencer, you can generate one on the spot in the format they need.
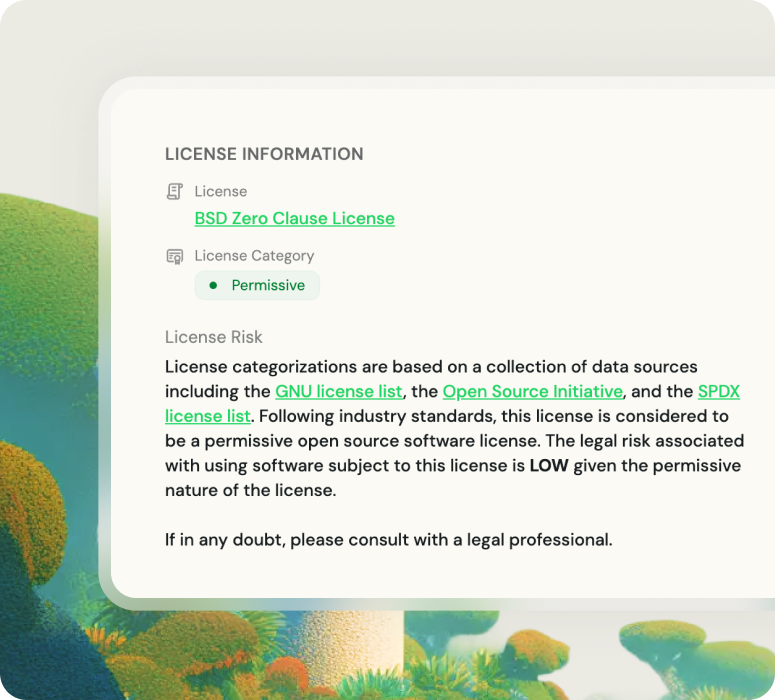
Strong copyleft licenses like GPL can create unexpected obligations in a commercial codebase. Fencer flags them early, before they can become a problem.
Most major compliance frameworks expect organizations to track and document their open source components. Fencer gives you a documented, always current inventory that supports your audit evidence without manual effort.

— Jason Byck
CTO, Renew